Introduction
Introduction
This is the overview of the project.
Introduction
In today’s digital landscape, ensuring the integrity and authenticity of digital certificates is paramount. Prominent institutions like the Institute of Engineering (IOE) are transitioning from traditional paper-based certificates to digital copies distributed directly to students’ preferred devices. This transition offers significant advantages in terms of accessibility, ef f iciency, and environmental sustainability. However, it also introduces critical challenges, particularly the risk of forgery and unauthorized alterations. Forgery, defined as the manipulation or alteration of digital documents for personal gain, poses a substantial threat to the credibility of academic institutions and their graduates. Such fraudulent activities can lead to severe consequences, including reputational damage for institutions and financial or professional losses for employers relying on forged credentials. Therefore, there is a pressing need for a robust system that ensures the authenticity and integrity of digital certificates. To address these challenges, our project explores two technological approaches: File Integrity Monitoring (FIM) and the InterPlanetary File System (IPFS). FIM is a security technology that monitors files for unauthorized modifications by comparing their current state to a known baseline using cryptographic hashes. While FIM provides real-time tamper detection, it relies on centralized storage systems that are vulnerable to single points of failure. In contrast, IPFS offers a decentralized solution that eliminates these vulnerabilities. IPFS is a peer-to-peer distributed file system that uses content addressing to store files immutably. Each file is assigned a unique Content Identifier (CID), which serves as its cryptographic fingerprint. This ensures that any attempt to alter the file will result in a mis match with its CID, making forgery virtually impossible. Additionally, IPFS’s decentralized architecture enhances scalability and resilience by distributing data across multiple nodes. After a comparative analysis of both approaches, we determined that IPFS is more re liable and better suited for implementing a secure certificate verification system. Conse quently, we adopted IPFS as the foundation of our solution and successfully implemented it in our system. The proposed system leverages IPFS’s capabilities to provide a scalable, tamper-proof platform for certificate verification. By integrating cryptographic hashing and decentral ized storage, our solution ensures that digital certificates remain authentic and immutable 1 throughout their lifecycle
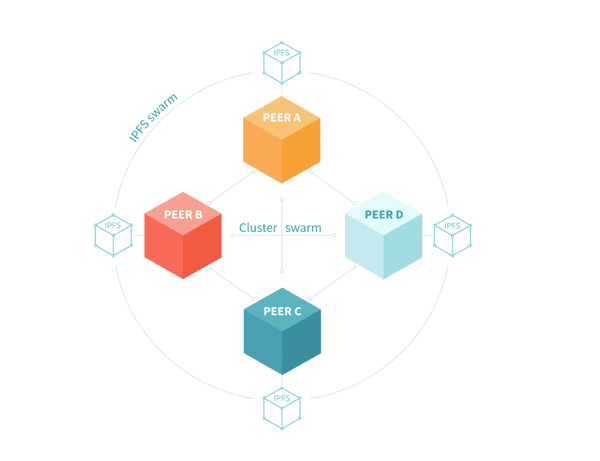
figure 1.1: IPFS Cluster
This report details the design, implementation, and evaluation of our IPFS-based cer tificate verification system. It demonstrates how this innovative approach addresses the limitations of traditional methods while meeting the growing demand for secure and efficient digital credentialing.
Background
In today’s digital landscape, ensuring the integrity and authenticity of digital certificates is paramount. With institutions like the Institute of Engineering (IOE) transitioning to digital certificates, the risk of forgery and tampering becomes a significant concern. Digital certifi cates are critical documents that verify academic achievements, professional qualifications, and other credentials. However, their digital nature makes them vulnerable to unauthorized alterations, which can lead to severe consequences for both individuals and institutions [1]. 2 The widespread use of digital editing tools has made it increasingly easy to manipulate digital documents, leading to potential fraud and misinformation. According to the Asso ciation of Certified Fraud Examiners, document fraud accounts for a significant portion of occupational fraud cases, resulting in substantial financial losses [1]. Therefore, there is a pressing need for robust systems that can verify the authenticity and integrity of digital certificates.
File Integrity Monitoring (FIM)
File Integrity Monitoring (FIM) is a security technology designed to monitor and detect changes in files that may indicate a cyberattack or unauthorized activity. FIM works by tak ing a cryptographic snapshot of files—typically through hash functions like SHA-256—and continuously comparing the current state of the file against the baseline hash [2]. Any discrepancy between the hashes suggests that the file has been altered. FIM is crucial for compliance with various regulatory standards, such as the Payment Card Industry Data Security Standard (PCI DSS) and the Health Insurance Portability and Accountability Act (HIPAA), which require regular monitoring of file integrity [3]. According to a Tripwire survey, organizations that employ FIM solutions detected breaches 96% faster than those that did not have such systems [4]. The general architecture of the FIM-based system is shown in Figure 3.1.
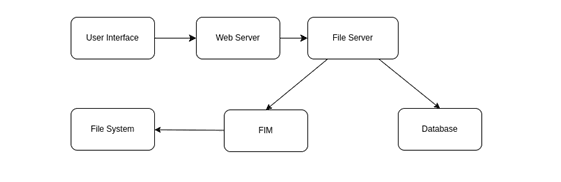
Figure 1.2: Architecture of the FIM-Based Document Verification System
Key Features of FIM:
• Real-Time Monitoring: Immediate detection of unauthorized changes allows swift response to potential security incidents.
• Audit Trails: Detailed logs of file changes support forensic analysis and compliance reporting.
• Automation: Modern FIM solutions integrate with Security Information and Event Management (SIEM) systems for automated alerts and responses.
Cryptographic Hash Functions
At the core of FIM is the use of cryptographic hash functions. These functions convert input data into a fixed-size string of characters that appears random. Properties of cryptographic hash functions include:
• Determinism: The same input will always produce the same hash output.
• Pre-image Resistance: It is computationally infeasible to reverse engineer the orig inal input from its hash.
• Collision Resistance: It is highly unlikely for two different inputs to produce the same hash output [5]
Common algorithms used include MD5, SHA-1, SHA-256, and SHA-3, SHA-256 being widely adopted due to its balance between security and computational efficiency [6].
InterPlanetary File System (IPFS)
The InterPlanetary File System (IPFS) is a peer-to-peer distributed file system that aims to fundamentally change the way information is distributed over the internet [7]. Unlike traditional HTTP protocols that rely on centralized servers, IPFS leverages a decentralized network where each node stores a collection of hashed files. The architecture of the IPFS based system is shown in Figure 5.1.
Key Characteristics of IPFS • Content Addressing: Files are identified by their cryptographic hash, ensuring that the content is immutable. Any change to the file results in a new hash. • Decentralization: Eliminates single point of failure, enhancing data availability and resilience. • Efficiency: Data are recovered from the closest node storing the content, reducing latency and bandwidth usage [8].
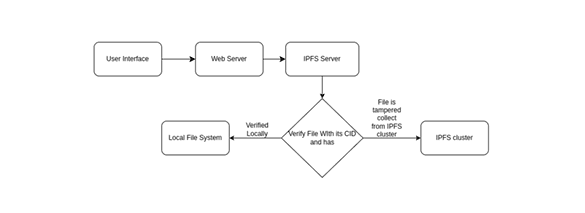
Figure 1.3: Architecture of the IPFS-Based Document Verification System
In 2022, IPFS has been adopted for various applications, including distributed web host ing, blockchain storage solutions, and decentralized applications (DApps), demonstrating its versatility and scalability [9]. IPFS for Document Verification • Immutable Records: Storing document hashes on a blockchain ensures a tamper proof record of the document’s state at a given time. • Transparent Verification: Any party can verify the authenticity of a document by comparing its hash to that recorded on the blockchain [10]. However, blockchain networks can face challenges such as scalability issues and high energy consumption, leading to the exploration of hybrid solutions that combine blockchain with decentralized storage like IPFS [11].
Cryptographic Hash Functions
Traditional methods for certificate verification include the following.
• Digital Signatures: Utilize asymmetric cryptography to sign certificates, providing authentication and non-repudiation [7].
• Public Key Infrastructure (PKI): Relies on Certificate Authorities (CAs) to issue digital certificates that authenticate the identity of entities.
• Centralized Databases: Organizations maintain internal databases to track and verify certificates. However, these systems are vulnerable to insider threats and cyber attacks.
Limitations of These Methods
Despite their wide adoption, traditional certificate verification methods face several limitations:
• Centralization Risks: Centralized systems are prone to single point failure and potential bottlenecks, making them less reliable in high-demand scenarios.
• Scalability Issues: Traditional systems struggle to efficiently handle large volumes of certificates, especially in academic or professional settings where thousands of certificates are issued annually.
• Trust Dependencies: These systems rely heavily on third-party authorities such as CAs, which can be compromised, leading to potential breaches of trust.
Advantages and Disadvantages of FIM and IPFS in Certificate Verification
FIM Advantages
• Real-time detection of unauthorized changes.
• Suitable for environments where immediate action is required.
• Integrates well with existing security infrastructures.
FIM Disadvantages
• If the file deletes from one server it can not be retrieved.
• If the database is altered or the server chrashes there is very small chances or retrieval .
IPFS Advantages
• Decentralized storage enhances availability and resilience.
• Content addressing ensures data integrity.
• Scalable solution for large datasets.
IPFS Disadvantages
• It is complicated and requires more resources.
• It requires continuous sync between different nodes for resources .
• Decentralized hash table needs to be maintained.
• More than one request needs to me made to retrive the orginal server containing the file.
By implementing systems using FIM and IPFS, this project seeks to leverage the strengths of both technologies to enhance document verification processes.
Join our Community Forum
Any other questions? Get in touch